The past decade has seen the journalism industry undergo a significant shift. As technology’s influence on our day-to-day lives has grown, so too has its impact on media, with today’s online environment requiring journalists to be well-versed in the art of digital security.
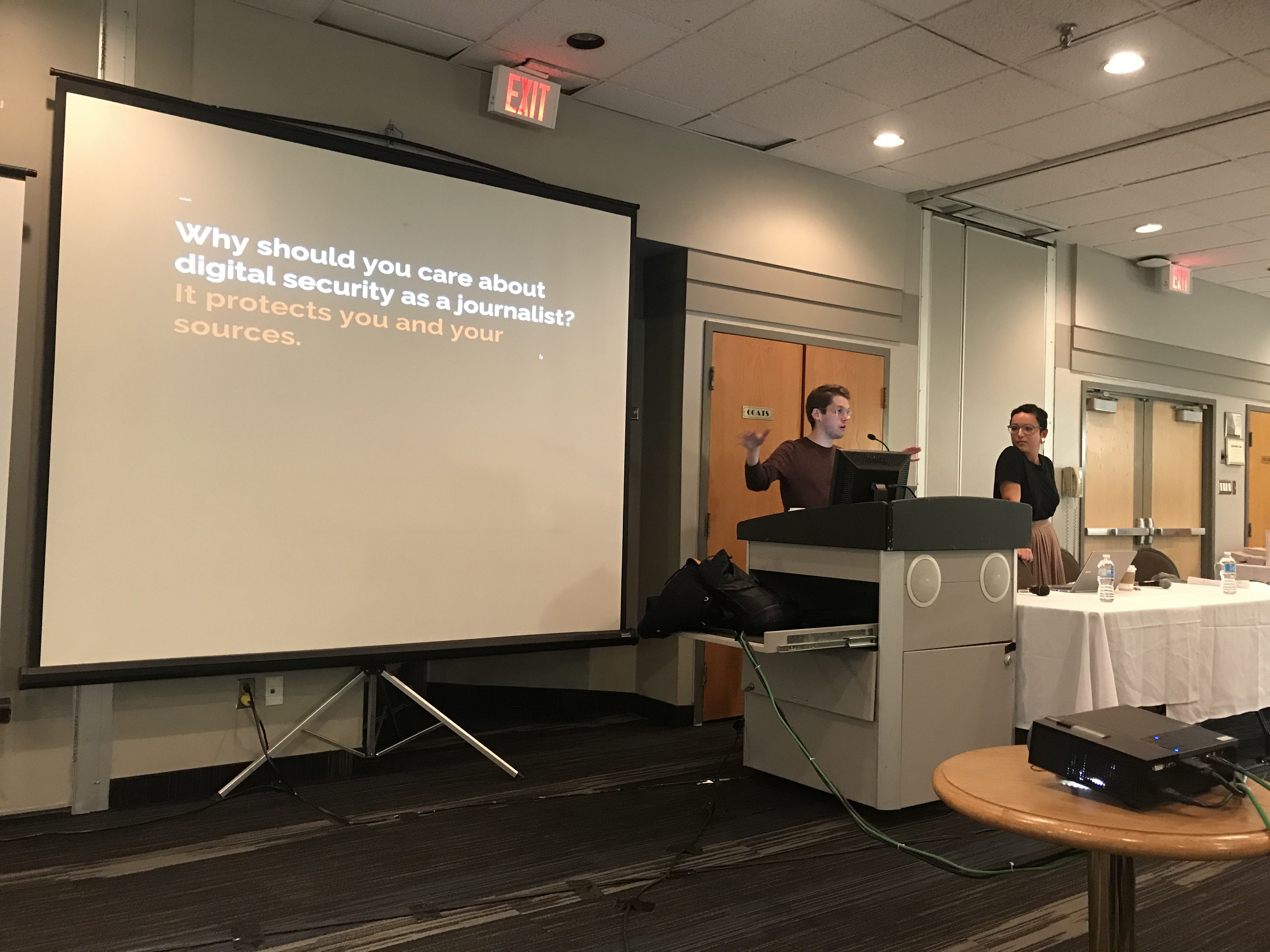
With that in mind, the Ryerson Review of Journalism hosted Matthew Braga, CBC News’ senior technology reporter, and Susana Ferreira, a producer with CBC’s The Current, as part of our two-day #MediaToo conference, where the pair led a presentation on this very subject.
Going over everything from how to begin thinking about cybersecurity to specific tools reporters should become acquainted with, Braga and Ferreira offered up plenty of tips to those in the crowd looking to stay protected online.
Here are five strategies the pair suggested to help journalists secure themselves and their sources online:
1. Understand the seriousness and uniqueness of the situation you’re in
There’s an endless array of tools and strategies available for those looking to beef up their digital security. But, according to Braga and Ferreira, finding the right ones is more a matter of understanding the situation you’re in rather than of simply seeking out the most advanced technology.
“There’s not a one-size-fits-all approach,” Braga said. “Every situation is different. You can’t just go to a workshop or read an article and then be done with it, because things are always changing. You always have to think about the situation you’re in, who you’re trying to protect.”
And while understanding that the tools you’ll need will be different depending on the circumstances, journalists should appreciate the potential risks of not staying secure.
“I’ve had conversations where people point out that they prefer to talk about ‘safety’ as opposed to ‘security’ because safety is more holistic and more encompassing,” Ferreira said. “A phishing attack, someone installing stalkerware, someone trying to get information from you or attack you digitally, can often lead to some sort of physical attack.
“So remember, this is something to be taken seriously and not just ‘Oh I don’t want someone reading my e-mails.’ It can actually escalate and have real-world consequences.”
“It can really run the gamut from someone being embarrassed if it was found out they were talking to a journalist, to someone losing their job, to someone getting jailed and beaten by the government, to assault and domestic abuse situations,” Braga added. “There’s a whole range of things that you might want to potentially take into account.”
2. Think of potential threats before you think of potential digital tools
One of the central strategies Braga and Ferreira discussed was threat-modelling—essentially trying to envision the potential threats you’re trying to combat so that you can understand what digital tools you need to use.
“Maybe you don’t know what particular tool you want to use, maybe you don’t know the name of an app or whether something exists that does what you need it to do in terms of protection, but knowing what your threat is and how to think of it, and how to think of the risks, can help guide you to what you actually need to do the job,” Braga said.
“The tools you use to protect you and one source in one situation might not be the same as another situation. They might be overkill in one situation, they might not be enough in another situation.”
Braga laid out five questions to keep in mind when going through that process:
1) What do I want to protect?
2) Who do I want to protect it from?
3) How bad are the consequences if I fail?
4) How likely is it that I will need to protect it?
5) How much trouble am I willing to go through to try to prevent potential consequences?
3. Change your online habits and practice operational security
The other key approach mentioned was practicing operational security, or opsec. While there are digital tools that can help you build up walls and cover your tracks, much of the battle online has to do with your own behaviour and understanding of the issues at hand.
“What operational security gets into is simply your habits,” Ferreira said. “Being safe, or being safer, with your information and other people’s information, is oftentimes a matter of just getting into the habit—the same way that you wouldn’t think of going to touch food without washing your hands.”
.@nowarian: Operational security (opsec) is like washing your hands before you touch food. “Practice good hygiene online,” she says.#MediaToo
— Review of Journalism (@ReviewofJourn) April 11, 2018
Ferreira gave an example of one editor who advised her staff, “Anything you write in an e-mail, don’t write it down unless you’re willing to have it broadcast in Times Square, over a loudspeaker to everyone. So that thing of ‘dance like no one’s watching’—e-mail like everyone’s watching.”
One easy way to engage in opsec and keep your information more secure is by compartmentalizing.
“Compartmentalization is literally having things in separate blocks that don’t quite touch each other,” Ferreira said. “If someone breaks into one thing, they can’t necessarily break into another if you have things sectioned off properly. Same thing with your behaviour.”
On a basic level, that might mean something like keeping separate social media profiles for your personal life and professional life, ensuring personal information isn’t as easily accessible.
4. Get acquainted with the different tools available, but don’t go overboard
Braga highlighted the Electronic Frontier Foundation’s Surveillance Self-Defense guide as a key resource to take some time with.
“It is one of the most valuable, useful things that I send to other journalists,” he said of the guide, which is a multi-section look at all things digital surveillance.
Resources from Digital Defenders and Toronto’s Citizen Lab were also highly recommended:
Along with the Surveillance Self-Defence guide (https://t.co/cju1jfJ0AF), @mattbraga and @nowarian suggest these two useful tools:
Citizen Lab’s Security Planner ➡️ https://t.co/MbCSORExkU
Digital First Aid Kit ➡️ https://t.co/6dozPWWydp#MediaToo
— Review of Journalism (@ReviewofJourn) April 11, 2018
But be cautious of some of the resources you’ve heard of most often, the pair said. Encryption, for example, is among the most discussed strategies recommended to those looking to enter the cybersecurity fray. But it might not always be necessary.
“Some people are going to be upset if I say this but it’s not always the way to go,” Ferreira said. “Encryption is very important, but when you have to encrypt your e-mails and decrypt e-mails, and you’re off travelling and you have devices specific to traveling, it becomes very complicated. You drop the ball, and it just becomes very frustrating.
“Part of what we’re trying to get at overall with this is that it’s not just ‘do this, do that and you’re set.’ It becomes a matter of almost wiring your behaviour to look at a situation and figure out how you should react to it and how you should adapt to try to make it as safe as possible.”
@FreedomofPress and @eQualitie help give journalists security training and @yoursosteam help women journalists in particular, says @nowarian #mediatoo @RyersonReview
— Maria Iqbal ماریہ (@maria9860) April 11, 2018
The same goes for free VPNs, a basic digital tool that many young internet users likely have some experience with. Braga said it’s important to keep in mind how companies who offer free tools operate.
“The problem with free VPNs [is], it’s like any kind of free thing on the internet like Facebook—because it’s free, they need to be able to support their service in some ways, they need to make money in some ways,” Braga said. “Oftentimes, that means tracking what you’re doing with the VPN and then selling that to advertisers and marketers.
“So you think you’re using the VPN to be secure and meanwhile the company that operates the VPN is actually packaging up your browsing history and selling it to people.”
.@mattbraga with some suggestions for useful digital tools at #MediaToo: pic.twitter.com/QOSxLSdu7T
— Review of Journalism (@ReviewofJourn) April 11, 2018
5. Try to encourage your sources, editors to be more secure online, too
Digital safety requires participation by all those involved, to a certain extent. Even the best tools available can be negated by less than ideal opsec practices by others involved in the editorial process.
“Even if you’re being very, very careful about how you’re conducting your interviews and how you’re trying to transmit information back to your editor, back to your producer or whoever at the newsroom—[problems can arise] if they don’t know how to handle it properly,” Ferreira said. “Your weakest link has got to be strong. And it just often is not good enough. So culture change is an important thing that a lot of people are trying to push for right now.”
.@nowarian on the need for industry-wide standards regarding cybersecurity training and resources:
“A lot of high-risk work is done by freelancers. Nobody has freelancers’ backs.”#MediaToo
— Review of Journalism (@ReviewofJourn) April 11, 2018
When it comes to your sources, it’s not as easy as telling them they have to use a specific app or website. It’s a negotiation, but even making things a little bit more secure is better than nothing. Try to understand their situation and adapt as necessary.
“Maybe you don’t have to convince [sources] to use the same digital safety tools,” Ferreira said. “Maybe they don’t have the capacity because their phone is old, or they don’t have a smartphone, or it’s too much of a risk for them. Or they just don’t want to—you can’t argue with that. You can meet in the middle, somewhere that’s still on the spectrum of safe, or safer.”
Communicating that need isn’t just a useful approach, it’s part of your duty as a journalist, added Braga.
“Part of your job as a journalist is making sure that when you’re working with a source, they know the risks of communicating with you in a certain way, of passing information to you in a certain way,” he said. “So if someone only wants to talk to you via e-mail, make it very clear to them as early as possible the risks of that—the risk to you and the risk to them.”
Watch the full video of Braga and Ferreira’s panel at Day 1 of the Ryerson Review’s #MediaToo conference here.